Ubiquiti EdgeRouter 配置 IPv6 設定實在摸不著頭緒,我相信許多大家遇到困擾,在默認情況下,照理來說 PPPoE 撥接連線後,應該會取得 IPv6 位址才對,不過這次還是需要指令開通它才能取得 IPv6 位址,根本玩弄巧成拙,之前試一下配置 IPv6 後,結果卻做了蠢事把事情弄糟糕~XD

對於管理上面,您必須會熟悉 SSH 指令,不過我們也可以從 Web CLI 指令,要確保一切正常是絕對必要的;若是在 Windows 上,我推薦用 PuTTY 客戶端。
基本指令
- 登入後,您可以使用下指令目前配置:show configuration
- 如果要更改配置,則需要下指令切換配置模式:configure
- 完成配置後,就可以應用套用:commit
- 若應用套用後,沒有顯示錯誤的話,可以保存生效:save
- 可以退出 configure 模式:exit
- 重新開機完成生效:reboot
事先準備
在之前,您手上準備有 PPPoE 用戶名和密碼,以下操作默認值:
- 適用型號:EdgeRouter 系列
- IP:192.168.1.1
- WAN:eth0
- 登入帳號密碼:UBNT / UBNT
防火牆建立 IPv6 規則
在 configure 終端輸入以下 Instruction list 內容:
configure
edit firewall
set ipv6-name WANv6_IN default-action drop
set ipv6-name WANv6_IN description “IPv6 packets from the internet to LAN and WAN”
set ipv6-name WANv6_IN enable-default-log
set ipv6-name WANv6_IN rule 10 action accept
set ipv6-name WANv6_IN rule 10 description “Allow established and related packets”
set ipv6-name WANv6_IN rule 10 state established enable
set ipv6-name WANv6_IN rule 10 state related enable
set ipv6-name WANv6_IN rule 20 action drop
set ipv6-name WANv6_IN rule 20 description “Drop invalid packets”
set ipv6-name WANv6_IN rule 20 log enable
set ipv6-name WANv6_IN rule 20 state invalid enable
set ipv6-name WANv6_IN rule 30 action accept
set ipv6-name WANv6_IN rule 30 description “Allow ICMPv6 packets”
set ipv6-name WANv6_IN rule 30 log enable
set ipv6-name WANv6_IN rule 30 protocol icmpv6
set ipv6-name WANv6_LOCAL default-action drop
set ipv6-name WANv6_LOCAL description “IPv6 packets from internet to router”
set ipv6-name WANv6_LOCAL enable-default-log
set ipv6-name WANv6_LOCAL rule 10 action accept
set ipv6-name WANv6_LOCAL rule 10 description “Allow established and related packets”
set ipv6-name WANv6_LOCAL rule 10 state established enable
set ipv6-name WANv6_LOCAL rule 10 state related enable
set ipv6-name WANv6_LOCAL rule 20 action drop
set ipv6-name WANv6_LOCAL rule 20 description “Drop invalid packets”
set ipv6-name WANv6_LOCAL rule 20 log enable
set ipv6-name WANv6_LOCAL rule 20 state invalid enable
set ipv6-name WANv6_LOCAL rule 30 action accept
set ipv6-name WANv6_LOCAL rule 30 description “Allow ICMPv6 packets”
set ipv6-name WANv6_LOCAL rule 30 log enable
set ipv6-name WANv6_LOCAL rule 30 protocol icmpv6
set ipv6-name WANv6_LOCAL rule 40 action accept
set ipv6-name WANv6_LOCAL rule 40 description “Allow DHCPv6 client/server”
set ipv6-name WANv6_LOCAL rule 40 destination port 546
set ipv6-name WANv6_LOCAL rule 40 source port 547
set ipv6-name WANv6_LOCAL rule 40 protocol udp
set ipv6-receive-redirects disable
set ipv6-src-route disable
commit
save
exit防火牆建立 IPv4 規則
再來一樣是在 configure 終端輸入以下 Instruction list 內容:
configure
edit firewall
set name WAN_IN default-action drop
set name WAN_IN description “WAN to internal”
set name WAN_IN rule 10 action accept
set name WAN_IN rule 10 description “Allow established/related”
set name WAN_IN rule 10 state established enable
set name WAN_IN rule 10 state related enable
set name WAN_IN rule 20 action drop
set name WAN_IN rule 20 description “Drop invalid state”
set name WAN_IN rule 20 state invalid enable
set name WAN_LOCAL default-action drop
set name WAN_LOCAL description “WAN to router”
set name WAN_LOCAL rule 10 action accept
set name WAN_LOCAL rule 10 description “Allow established/related”
set name WAN_LOCAL rule 10 state established enable
set name WAN_LOCAL rule 10 state related enable
set name WAN_LOCAL rule 20 action drop
set name WAN_LOCAL rule 20 description “Drop invalid state”
set name WAN_LOCAL rule 20 state invalid enable
commit
save
exitMSS 值更改
由於 MSS 默認值是 1412,可能有時無法正常解析以及巨大封包異常,所以需要調整此值,這非常很重要。
set firewall options mss-clamp mss 1452建立 WAN 端口對應 PPPoE
除了 PPPoE 設置 IPv4 之外,也額外增加對應 IPv6 撥接出去。
- set pppoe 0 user-id:PPPoE 帳號,如有申請浮動轉固定IP者,請輸入 @ip.hinet.net
- set pppoe 0 password:PPPoE 密碼
configure
edit interfaces ethernet eth0
set description “Internet (PPPoE)”
set duplex auto
set firewall in ipv6-name WANv6_IN
set firewall local ipv6-name WANv6_LOCAL
set pppoe 0 default-route auto
set pppoe 0 mtu 1492
set pppoe 0 name-server auto
set pppoe 0 user-id ********@hinet.net
set pppoe 0 password ****************
set pppoe 0 dhcpv6-pd pd 0 interface switch0 prefix-id :0
set pppoe 0 dhcpv6-pd pd 0 interface switch0 service slaac
set pppoe 0 dhcpv6-pd pd 0 prefix-length /64
set pppoe 0 firewall in name WAN_IN
set pppoe 0 firewall local name WAN_LOCAL
set pppoe 0 ipv6 dup-addr-detect-transmits 1
set pppoe 0 ipv6 enable
commit
save
exit建立 NAT 服務封包對應
這是必須建立,若沒建立的話,封包出不去的。
configure
edit service nat rule 5010
set description “Masquerade for WAN”
set outbound-interface pppoe0
set type masquerade
commit
save
exitDNS 服務器轉發設置
我利用 EdgeRouter 充當 DNS 轉發器,在各別台 LAN IP上網發送 DNS 請求,並將這些請求會轉發到您指定的 DNS 服務器。
show dns forwarding nameservers
configure
set interfaces ethernet eth0 dhcp-options name-server no-update
set interfaces ethernet eth0 dhcpv6-pd no-dns
set service dns forwarding name-server 1.1.1.1
set service dns forwarding name-server 1.0.0.1
set service dns forwarding name-server 2606:4700:4700::1111
set service dns forwarding name-server 2606:4700:4700::1001
set service dhcp-server shared-network-name LAN subnet 192.168.1.0/24 dns-server 192.168.1.1
commit
save
exit再一次輸入 show dns forwarding nameservers 目前狀態,就可看到已變更成功。
show dns forwarding nameservers
———————————————–
Nameservers configured for DNS forwarding
———————————————–
1.1.1.1 available via ‘statically configured’
1.0.0.1 available via ‘statically configured’
2606:4700:4700::1111 available via ‘statically configured’
2606:4700:4700::1001 available via ‘statically configured’
———————————————–
Nameservers NOT configured for DNS forwarding
———————————————–
168.95.192.1 available via ‘ppp pppoe0’
168.95.1.1 available via ‘ppp pppoe0’
2001:b000:168::1 available via ‘system’
2001:b000:168::2 available via ‘system’雖然還有其它幾種方法可以實現 IPv6,但是這也是最簡單的轉發方法。
ICMPv6 開通方法
為了讓 ICMPv6 流量導入,需要把 ICMPv6 開通,以下依 Windows 10 操作為例。
點選 開始 → 執行 輸入 wf.msc 呼叫 Windows Defender 進階防火牆視窗,輸入規則 → 新增規則

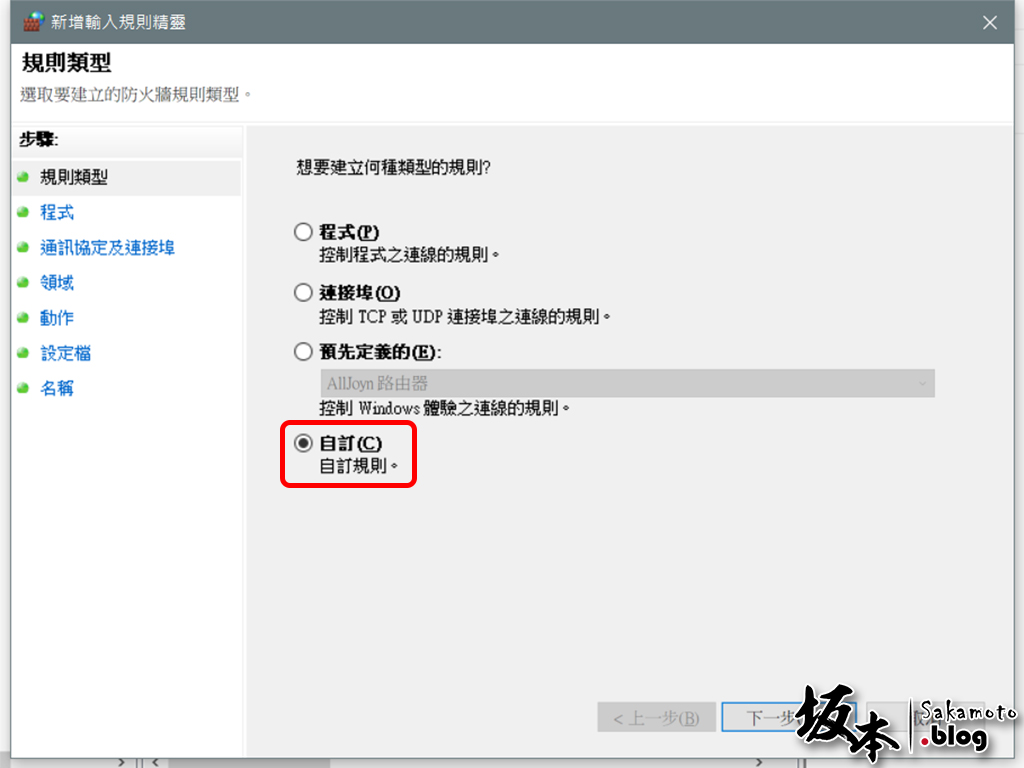
在規則類型,選擇 自訂
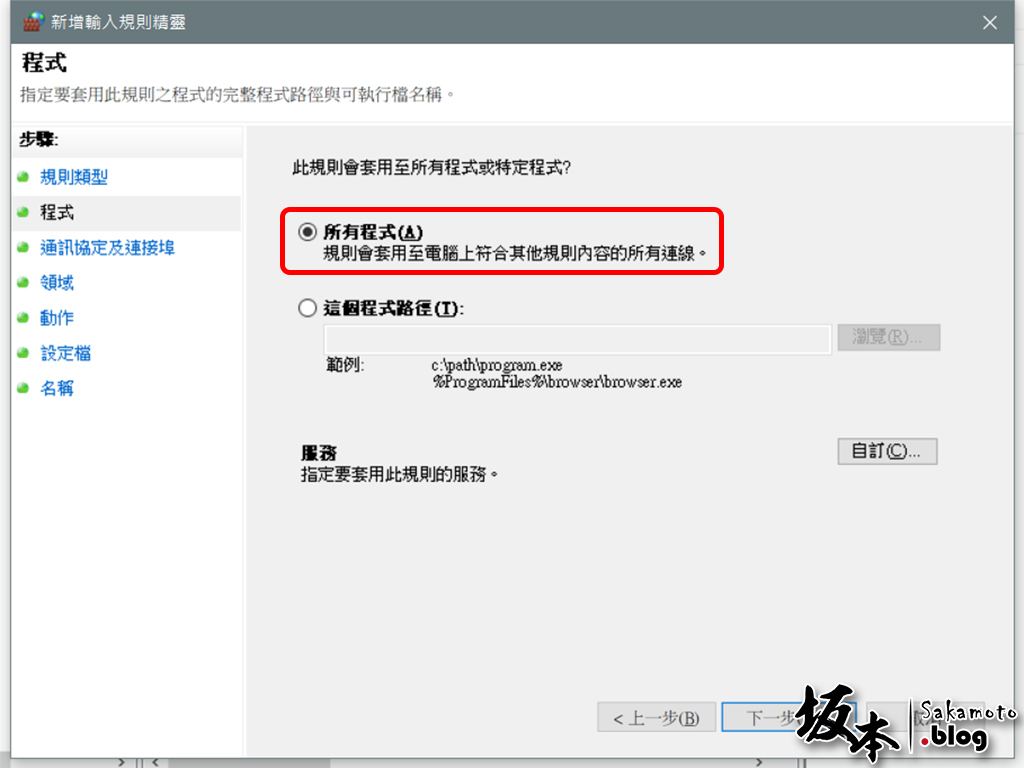
選擇 所有程式
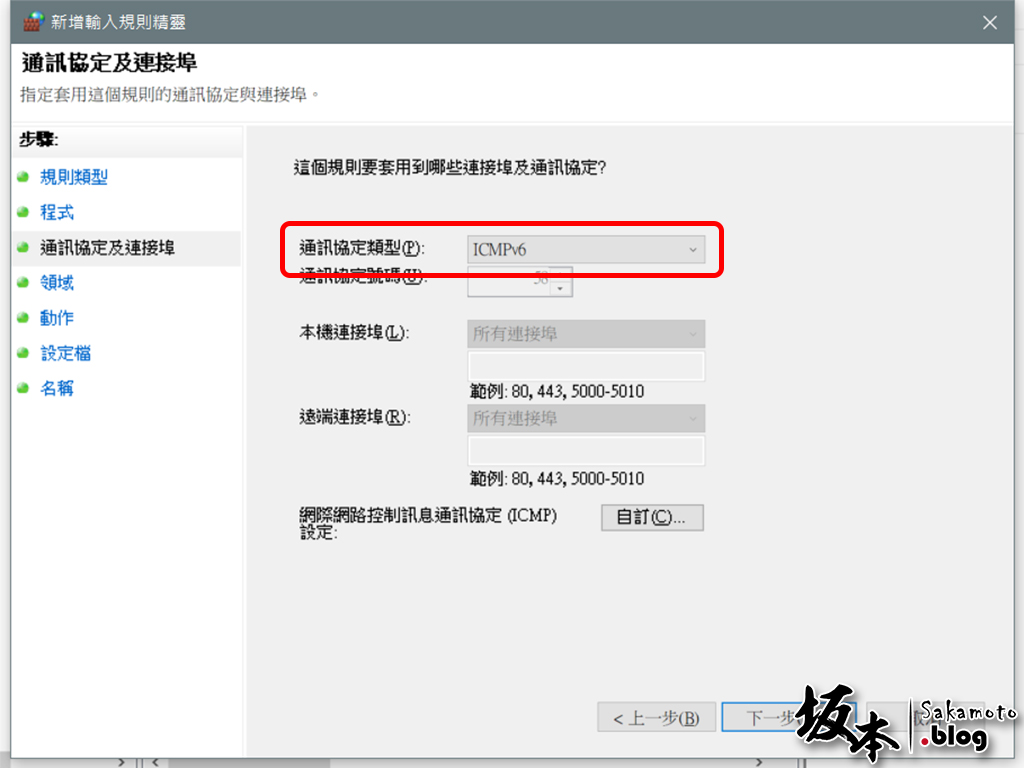
通訊協定及連接埠,選擇 ICMPv6
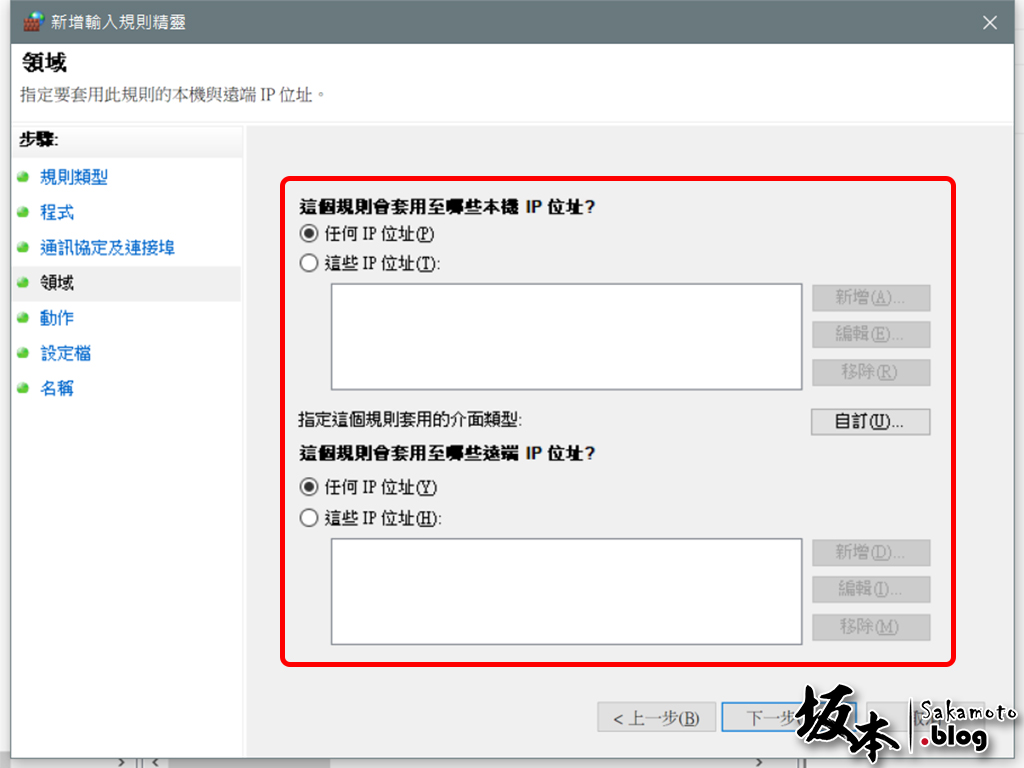
領域規則 IP 位址部分,選任何 IP 位址連通
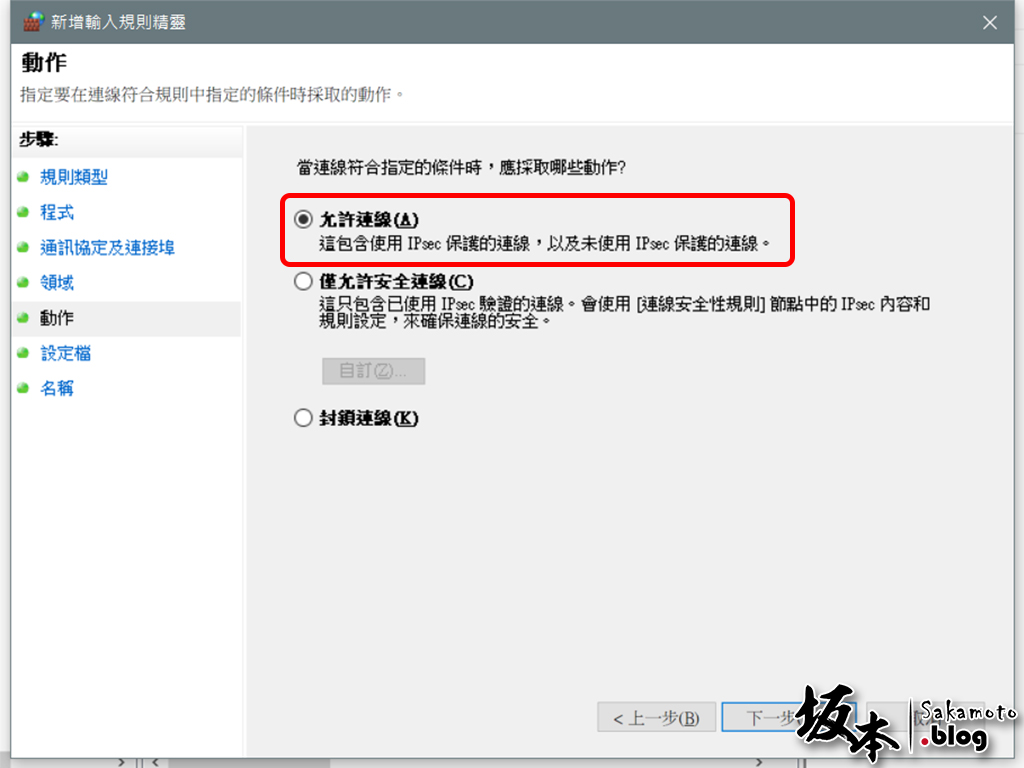
連線符合規則條件,選擇 允許連線
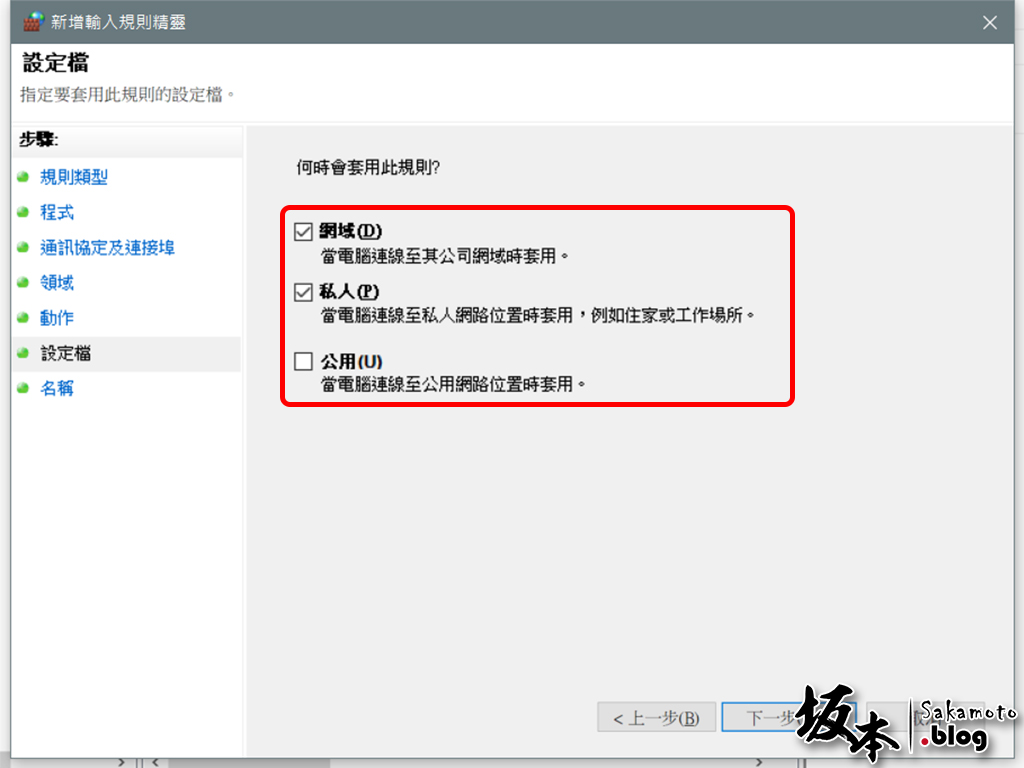
此為設定檔要套用那些規則,依您需求,若不清楚的話,可以全部選勾
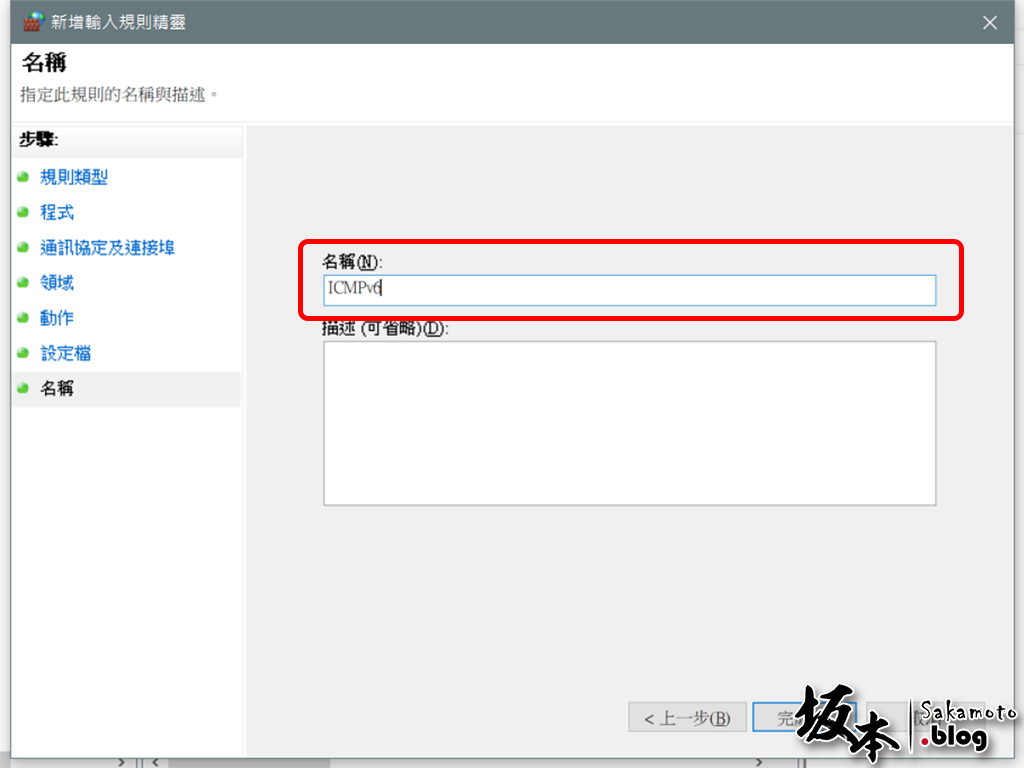
輸入名稱,由您喜好命名,例如:ICMPv6 ,點 完成 就生效囉~
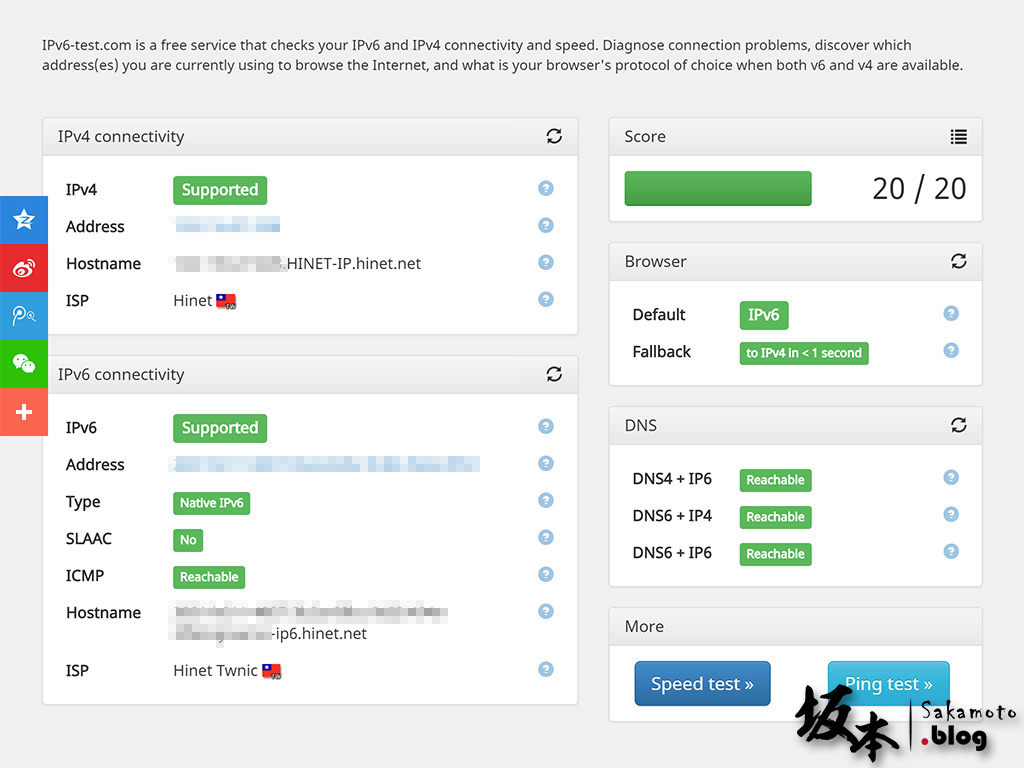
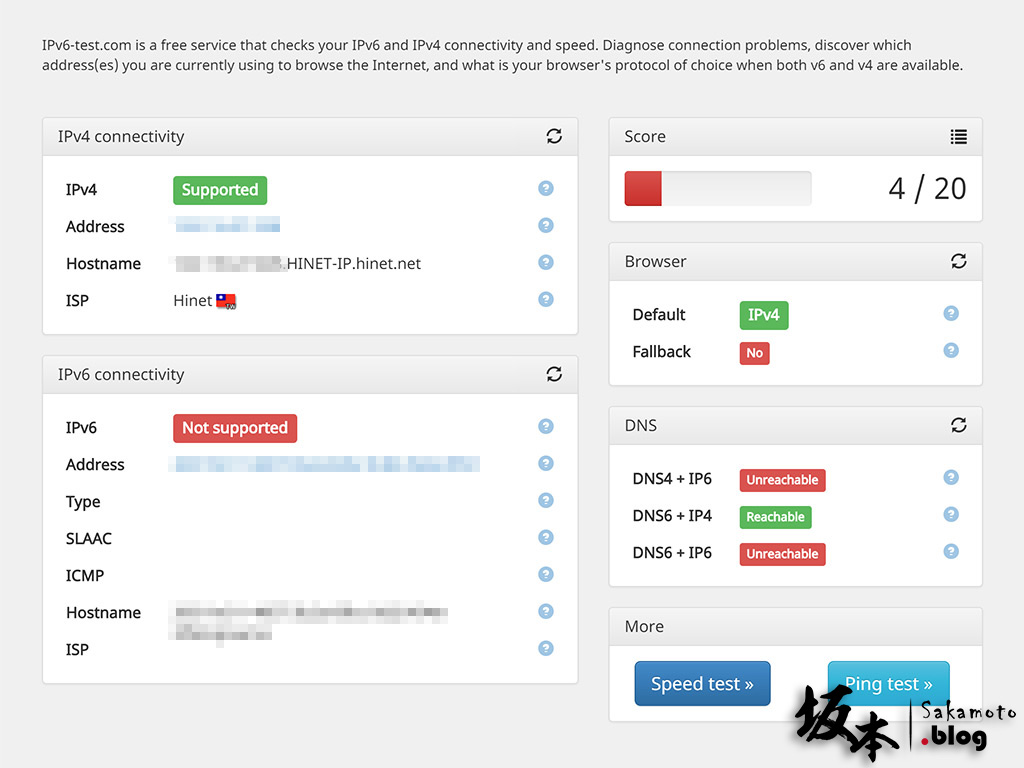
實際測試
以下二個網站測試 IPv6 狀態: